The Compound Vulnerability
Compound loading: when multiple forces act on a structure simultaneously, the failure threshold drops. Chinese intelligence inside telecom networks. Federal cybersecurity capacity dismantled from within. A still-active adversary operating inside systems that haven't been remediated.

There's a concept in structural engineering called compound loading: when multiple forces act on a structure simultaneously, the result isn't simply additive. The failure threshold drops. A column that would hold under vertical load alone, and would hold under lateral load alone, fails at a point neither force would have reached on its own. The structure doesn't collapse because of the first force or the second. It collapses because both forces are present at once, and the combination creates a condition the structure wasn't designed to survive.
I've been thinking about that concept for most of 2025, in the context of what I described in the two preceding essays. I keep reaching for structural metaphors because the failure pattern here is structural in exactly that sense: not a single catastrophic event but a combination of conditions that has moved the overall security posture to somewhere we haven't been before, and that the existing frameworks for understanding cybersecurity risk don't quite capture.
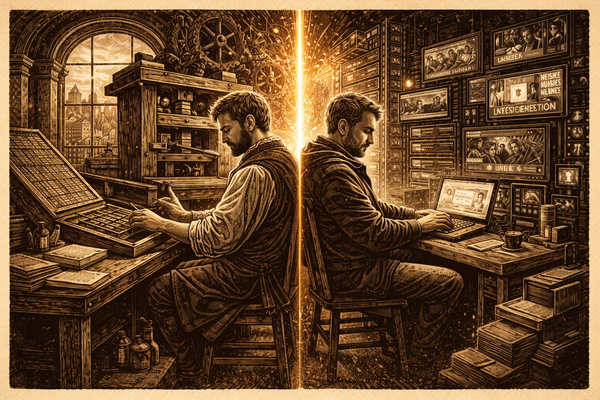
What the first essay described was an external force: Chinese state-sponsored hackers occupying the communications infrastructure of the United States for years, through vulnerabilities that basic discipline would have closed. What the second essay described was an internal force: the deliberate dismantlement of the monitoring, oversight, and response capabilities that would detect and limit the damage from intrusions, combined with the creation of new attack surfaces through uncontrolled access to the most sensitive non-military data repositories in the federal government. Two forces. Both present. Acting simultaneously on a structure already under stress.
Adding those two threats together and calling the result "the compound vulnerability" undersells what the combination actually does to the defense. The relevant question isn't the magnitude of each threat. It's what the defense looks like when both are simultaneously true.
Let me try to make the structural argument precise, because it's easy to describe this as "things are bad and getting worse" without specifying why the combination is worse than either condition alone.
Consider what a functioning security posture looks like in the face of a sophisticated external adversary. You have defenders who understand what they're protecting. You have monitoring systems that detect anomalous activity. You have incident response teams who can investigate, contain, and remediate when something gets through. You have intelligence about what the adversary is doing and how they're operating. You have a regulatory framework that enforces minimum standards on the organizations responsible for critical infrastructure. And when an intrusion happens anyway, because it will happen, you have the institutional capacity to find it, study it, and build better defenses from what you learn.
That's the system. Not perfect, but functional. The Cyber Safety Review Board was created precisely to embody one part of it: post-incident analysis by multi-agency, multi-sector experts who could issue public findings and make systemic recommendations. It had previously investigated the SolarWinds attack and the Log4j vulnerability, producing assessments that informed real improvements. When Salt Typhoon was discovered, the CSRB opened an investigation.
In January 2025, the Trump administration dismissed all members of the CSRB before that investigation could be completed. The board has not been reconstituted. There will be no public after-action report on one of the most significant intelligence penetrations in American history.
That's one element. Now stack it alongside what the preceding essays documented in detail: CISA losing nearly a third of its workforce including both red teams and most of its senior technical leadership. The FCC rolling back the security requirements it had imposed on carriers after Salt Typhoon, at the carriers' lobbying. DOGE personnel accessing the most sensitive government databases with disabled logging and unvetted devices, while the monitoring systems that would have flagged the anomalous access were switched off and the whistleblower who documented what he'd seen was threatened into silence.
Lay all of those conditions beside each other. This is the compound vulnerability: weakened external defenders, weakened internal oversight, enlarged attack surface, reduced detection capability, suppressed incident reporting, and a still-active adversary operating inside systems that haven't been remediated. Each condition on that list is a serious concern in isolation. Together they interact, and the interaction is the point.
The pattern underlying all of it is one I've watched play out in organizational contexts throughout my career, though rarely at this scale and never in these two directions at once. In both cases, the defense eroded through accumulated choices that each seemed individually defensible and collectively produced something no one designed. The result isn't intended. But intention doesn't determine outcome, and from the adversary's perspective, intention is irrelevant. What matters is the condition of the defense they find.
China's approach to the United States in cyberspace has shifted significantly over the past decade. Professor Ciaran Martin, former head of the UK's National Cyber Security Centre, described the shift in early 2025 this way: China has moved from opportunistic to strategic, and from passive to active. It no longer just spies and steals; it has laid the groundwork for disruptive operations against Western critical infrastructure. Salt Typhoon is the intelligence-collection face of that strategy. Volt Typhoon, which pre-positions inside aviation systems, water utilities, energy infrastructure, and transportation networks, is the disruption-capability face. Both operate through the same mechanism: finding the defenders who haven't maintained discipline and establishing persistence before the access is noticed.
In March 2025, Volt Typhoon breached Littleton Electric Light and Water Department in Massachusetts, a small utility, not an obvious high-value target, but exactly the kind of node that a strategy of broad pre-positioning requires. The same month, DHS documented that Salt Typhoon had stolen 1,462 network configuration files from approximately 70 U.S. government and critical infrastructure entities across 12 sectors, including energy, communications, transportation, and water. Those configuration files are a detailed map of how those networks are structured, where the access points are, what the traffic patterns look like. The intelligence value isn't just what happened in the breach; it's what the breach makes possible next.
"If the PRC-associated cyber actors that conducted the hack succeeded," a DHS memo noted about the Army National Guard compromise in this same period, "it could hamstring state-level cybersecurity partners' ability to defend U.S. critical infrastructure against PRC cyber campaigns in the event of a crisis or conflict."
That sentence is worth reading carefully. Causing damage now would reveal the access and trigger a response. The actual objective is positioning: to be where you need to be when the moment comes, while simultaneously degrading the capacity of the people who would respond to that moment.
The DIGOS breach reported today in Italy fits the same template precisely. Between 2024 and 2025, hackers linked to Chinese state intelligence penetrated the Italian Interior Ministry's network and extracted the identities of approximately 5,000 DIGOS agents (names, roles, operational postings), the officers responsible for Italy's most sensitive investigations: counter-terrorism, organized crime, and the surveillance of Chinese dissidents living in Italy. The intrusion was described by Italian investigators as "surgical": not oriented toward disruption or sabotage, but toward selective extraction of strategic information. The objective, according to sources familiar with the dossier, was to know in advance who investigates what, where, and with what priorities.
What makes the timing particularly difficult to set aside is the diplomatic context. During the same months the intrusion was apparently underway, Beijing was simultaneously pursuing a policy of judicial cooperation with Rome, offering, for the first time, a response to an Italian rogatory from the Prato prosecutors office, and sending a delegation to meet with Italian law enforcement on organized crime. Cooperation offered formally. Intelligence collected operationally. Both at the same time. Italian authorities reportedly froze joint patrols with Chinese officers and suspended training programs once the breach became known. The cooperation channel, carefully constructed over years, collapsed when the picture became clear.
The pattern Professor Martin described, strategic rather than opportunistic, positioning rather than immediate exploitation, is running on multiple continents simultaneously. The OPM breach mapped the American national security workforce. The DIGOS breach mapped the Italian internal security workforce, with particular attention to the agents tracking Beijing's critics abroad. The architecture is the same. The targets are the people whose job it is to know what China is doing. Knowing who they are, where they work, and what they're currently investigating is its own form of leverage, independent of any operation that leverage might eventually enable.
The two failures described in the earlier essays aren't separate stories that happen to be occurring at the same time. They share a root.
I described that root in the preceding essays: the performed security of the telecom carriers and the contempt for security protocols that characterized the DOGE access are different mechanisms producing the same structural outcome. Neglect and velocity arrive at the same place. The adversary doesn't distinguish between a door left open through indifference and a door propped open through impatience. What matters is the door.
But the compound vulnerability is not just both doors being open at once. It is what happens to the building when both doors are open and the security desk is unmanned and the cameras have been switched off and the person who noticed the intrusion was told to stop talking about it. The interaction between the conditions is where the actual danger lives, and the interaction produces something that neither condition produces alone: an environment in which the adversary can operate and no one remaining has the visibility to know whether they are operating.
There's a version of this observation I've been reluctant to state directly and probably shouldn't avoid. The conditions that foreign intelligence services have spent enormous resources trying to manufacture from the outside were created domestically, through official channels, in a matter of months. Whatever the intent behind those actions, the effect on the adversary's operating environment is not ambiguous. It improved substantially in 2025, while the defense's operating environment deteriorated substantially. Those two facts are not independent.
Something I find genuinely difficult to assess, and want to be honest about, is the extent to which the compound effect is recoverable.
In structural engineering, once a structure has crossed its failure threshold under compound loading, it doesn't return to its original state when you remove one of the forces. The failure changes the structure. Some of what's been lost in the past year falls into that category. The CSRB investigators who were dismissed don't simply reconstitute their institutional knowledge when the board is reassembled. The CISA analysts who left, the best technical talent the government had recruited in years, people who had documented their expertise across years of federal service, took that knowledge with them, and some won't return. The training pipelines that produced the next generation of threat hunters were disrupted at their development stage. The former NSA cybersecurity director Rob Joyce was explicit about this: eliminating probationary employees destroys the developmental programs that produce the specialized skills the defense requires. You can hire people back. You can't hire back the years of formation.
The data that moved is also gone. Social Security records copied to Cloudflare cannot be un-copied. Whatever the Russian actors who attempted to log into the NLRB systems within fifteen minutes of credential creation were doing with those credentials, that probing happened. The Salt Typhoon network configuration files are in the hands of the Ministry of State Security. The CALEA access, the intelligence about who was under investigation through which carrier, whatever was observed during the years the operation was running: that intelligence was collected. It informed decisions that were made. It will inform future decisions.
Against all of that, the recoverable elements: the regulatory framework can be rebuilt, though the political conditions that enabled the FCC rollback haven't changed. CISA can be rebuilt, though rebuilding institutions after rapid dismantlement takes years and the threat doesn't pause while you rebuild. The DOGE access can be revoked, closed by court order or changed by policy, though the data that moved before revocation has moved.
Recovery is possible. What's less clear is whether it's the same structure you're recovering to, or a structure that has absorbed permanent changes from the loading it experienced.
There's one more structural element I want to name, because it sits underneath both failures and connects to the larger argument the preceding series made about formation and discernment.
The public cannot evaluate any of this. A citizen who wants to know whether their telecommunications infrastructure is secure from Chinese intelligence cannot determine that, because the carriers have refused to provide documentation and the FCC has chosen not to require it. A federal employee who wants to know whether their security clearance investigation file was accessed and where it went cannot determine that, because the logging was disabled before the access occurred. A whistleblower who observed what appeared to be a major security incident and reported it through the proper channels was told to drop the investigation, and was later found to have been placed under physical surveillance.
The public's relationship to the security of the systems they depend on is mediated entirely by institutions whose transparency has been, in both cases, either absent or actively obstructed. The telecoms won't say. The government won't require them to say. The government's own systems were accessed through channels that bypassed accountability mechanisms, and the accountability mechanisms that would document what happened were the first things disabled.
I said in the earlier series that discernment, the capacity to evaluate the difference between genuine security and performed security, requires formation. You have to know enough about what the real thing looks like to recognize when you're being offered a substitute. The public doesn't have that formation in cybersecurity, and the institutions that would either maintain genuine security or tell the truth about performed security have, in the situations I've been describing, done neither.
That's not a political observation. Or rather, it's only incidentally one. It's primarily an epistemological observation about the conditions under which the public can know anything about whether the systems they depend on are safe.
They currently can't. And the structural condition that makes it impossible, the combination of inadequate security, insufficient transparency, and disabled accountability, is exactly what a sophisticated adversary would construct if it could.
It didn't need to.
The Compound Vulnerability is the third essay in the series of the same name.
Sources
U.S. Government Primary Sources
Official statements, advisories, and sanctions:
- CISA/NSA/FBI Joint Advisory (Feb 2024): "PRC State-Sponsored Actors Compromise and Maintain Persistent Access to U.S. Critical Infrastructure" — confirms Volt Typhoon in communications, energy, transportation, and water systems with "at least five years" of access. Available at cisa.gov and media.defense.gov.
- U.S. Treasury OFAC Sanctions (Jan 17, 2025): Sanctioned Sichuan Juxinhe Network Technology for "direct involvement" with Salt Typhoon. Confirms Salt Typhoon compromised network infrastructure of multiple major U.S. telecom and ISP companies. treasury.gov/news/press-releases/jy2792
- Congressional Research Service (Congress.gov): Salt Typhoon report IF12798 — confirms nine U.S. telecom companies compromised, CALEA lawful intercept systems accessed, PRC state sponsorship via Ministry of State Security.
- DHS Declassified Memo (released July 2025): Salt Typhoon stole 1,462 network configuration files from ~70 U.S. government and critical infrastructure entities across 12 sectors between January and March 2025. Includes the Army National Guard quote about hamstringing state-level cyber defense.
- FBI (August 2025): FBI Cybersecurity Division director Brett Leatherman confirmed Salt Typhoon targeted 80+ nations, 600+ organizations notified. $10 million bounty announced April 2025.
- Senate Commerce Committee Hearing (Dec 3, 2025): Senator Cantwell's hearing with telecom and cybersecurity experts. Confirms carriers still cannot prove Salt Typhoon has been eradicated. FCC rolled back security requirements November 20, 2025. Both AT&T and Verizon failed to provide remediation documentation when requested.
Industry/Cybersecurity Firm Reports
Ongoing monitoring:
- Recorded Future / Insikt Group (Feb 2025): Salt Typhoon still active, observed seven compromised Cisco devices communicating with Salt Typhoon infrastructure on five telecom networks between December 2024 and January 2025. Targeted 1,000+ unpatched Cisco edge devices globally.
- Dragos Annual OT Report (Feb 2026): Volt Typhoon "still very active" and "absolutely mapping out and getting into embedding in U.S. infrastructure, as well as across our allies." CEO Rob Lee stated some compromised sites "we will never find." Volt Typhoon was in Littleton Electric Light & Water for 10 months before discovery.
- Trend Micro: Salt Typhoon attacks confirmed across critical infrastructure worldwide, not limited to U.S.